I can therefore resort to the flip of a coin to generate random binary numbers: if it’s heading, the extracted digit will be 0, if it's tails it will be 1. Thus the string of results HHHTTTTHTHT becomes 00011110101, an unpredictable string of 0 and 1 in completely random positions; a string of "bits", of "binary digits", the numerical base on which all electronic devices "count".
Random bit strings correspond to random numbers, including primes that can only be divided by themselves - like 3, 5, 7, 11, etc. It is from enormous prime numbers that cryptographic keys are built to protect our digital life. The more certain the randomness, the greater the security of the keys that protect our data, our photos, social accounts, bank transactions and health data. Virtually everything is entrusted and transmitted over the network. In addition to our data protection systems, random bit streams are now essential in gaming, gambling, virtual reality, numerical simulations of complex systems and the Internet of Things.
Coins aside, how can I generate, perceive and verify randomness?
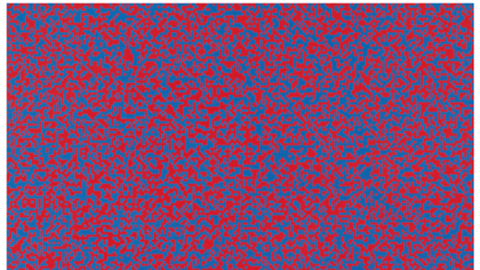
This 1960 work by François Morellet is one of the finest representations of chance. Morellet asked his family to randomly open the New York telephone directory and read a phone number: if it ended with an even digit, he painted a box red, if it was odd, he painted it blue.
It is easy for our eyes to perceive randomness when it is represented as Morellet did: in his paintings, no pattern can be seen, and the sequences of 40,000 pixels show no structure. Otherwise, a malevolent hand would have altered the randomness, with a pinch of determinism and external control, allowing the observation of one part of the picture to predict what might appear in another part.
Beyond the system used by Morellet, the most common method of generating random numbers is using sophisticated algorithms.
This method is very fast, cheap and relatively easy, but:
- The software that generates the random numbers could have errors, bugs;
- The recipe used could have a backdoor, a back door through which to spy on the generation and perceive what could be the next generated figure, breaching the protection scheme;
- § If I could know what numerical "seeds" were used to initialize the algorithms, I would know the whole sequence of the generated digits.
But, even if the architecture of the algorithm were perfect and the seeds were well preserved, there would still be an underlying, irreducible problem: algorithms are deterministic structures and extracting randomness from a deterministic process is an oxymoron, a contradiction. This observation led John Von Neumann, one of the founding fathers of Information Science, to affirm: "Anyone who considers arithmetical methods of producing random digits is, of course, in a state of sin".
It is possible to overcome these limitations by resorting to the analysis of phenomena which, due to their complexity or nature, produce unpredictable results, just like our currency.
However, a coin can be rigged, altering the probability of getting 0 or 1, which can happen for any phenomenon governed by classical physics. Random is real and beautiful, but fragile. However, if I pass to the microscopic world, to the structure of matter and enter the domain of quantum mechanics, it will be the very essence of Nature that protects me: at every moment the world chooses one of the infinite possible evolutionary paths and which one it will take cannot be conditioned. Some worlds are more probable than others but there is an intrinsic, irreducible impossibility of predicting what will happen and when it will happen. An example is provided by unstable nuclei: in a radioactive material one element of the periodic table changes into another but we cannot predict when it will happen and which of the nuclei will transform. It will happen randomly.
The decay of radioactive nuclei, where the transformation is accompanied by the emission of sub-atomic particles, alpha, beta or gamma rays, was the quantum phenomenon first used to generate random state bits.
Let’s suppose that some detectors "see" the particles emitted during a decay: like Morellet, I could count the number over a while. If the number is even, the value of the bit will be 0, if odd, 1. Robust, simple, quantum but impractical and inefficient: nobody wants to keep a radioactive source in their pocket and if I want 1 and 0 to have the same probability the number of particles would have to be big and I would "consume" many events to generate a single bit.
Random Power, the start-up established based on the intuition of Massimo Caccia, Professor of Experimental Physics at the University of Insubria in Como, is based on the same principle, but without radioactivity: the impulses do not correspond to the detection of nuclear particles but to electrical impulses, self-amplified, inside dedicated Silicon structures. The impulses are triggered by single electrons which, due to the quantum nature of Silicon and the fact that we do not live in a world frozen at absolute zero, in an unpredictable way jump to energy levels that release them from the atom they belong to. Being affected by a very strong electric field inside the Silicon, they impact other atomic systems, freeing other electrons which, in a real avalanche process, originate a detectable current signal in one billionth of a second. By identifying when the process occurs with an accuracy of no less than one billionth of a second and analysing the temporal sequence of events, bits can be generated in a silicon pill.
From the quantum nature of silicon to bits, from these to random numbers and then to the generation of cryptographic keys, the course of events is traced to generate an inviolable quantum shield and supply the most revolutionary technologies for cyber security. The value of the project has been recognised and rewarded for the second time by the European Union as part of the ATTRACT project container, where the start-up, together with a task force of European partners aims to develop, within three years, a platform of advanced cybersecurity systems. An ambitious goal but an extremely valuable consortium, which led to the team getting significant funding at the end of an extremely selective competitive evaluation process: 1,211 proposals were presented in “Phase 1”, for the pilot project; 170 were selected, of which only 87 submitted a “scale-up project” for a “Phase 2”; only 18 projects were considered worthy, including the one linked to Random Power.
SECO – the centre of excellence in the field of technological innovation, Internet of Things and Artificial Intelligence - and E4 Computer Engineering, the partner appointed to manage System Integration and Commissioning, will collaborate in the development of a multi-generator board that will be applied to the infrastructures of a data centre. The hardware will consist of a pulse generator and a disjoint chip, designed by the French company WEEROC, which reads and processes the signals emitted by the generator.
At the same time, thanks to the contribution of IMASENIC, a Spanish chip design company and the NAGRAVISION - KUDELSKI Group, a monolithic chip will be created that integrates the generator and the analysis functions of the impulses generated in a single solution, for applications in the IoT, automotive and communications fields. The IRIS group of the Bruno Kessler Foundation will participate in this phase of the project, which will focus in particular on the design of the heart of the device, the matrix of “cells” that originate the impulses distributed randomly over time.
Finally, the consortium will work on the development of agnostic applications, which facilitate the use of the hardware that is being designed, to be able to provide a Root of Trust, the certified "root" of every cryptographic process.
The project officially started on 15 May 2022, with a duration of 26 months and with a well-integrated team hitting the ground running.